All articles
How AI Attacks are Driving CISOs to Swap Old Prevention Tactics for Resilient Data and Provable Recovery
Rick Orloff, VP and CISO at Everpure, shares how embedding security in core data infrastructure gives enterprises control when attacks inevitably break through.
Resiliency is the security lens. It's not about checking the right boxes. It's about whether we can take our data, operate somewhere else, and how quickly we can do it.

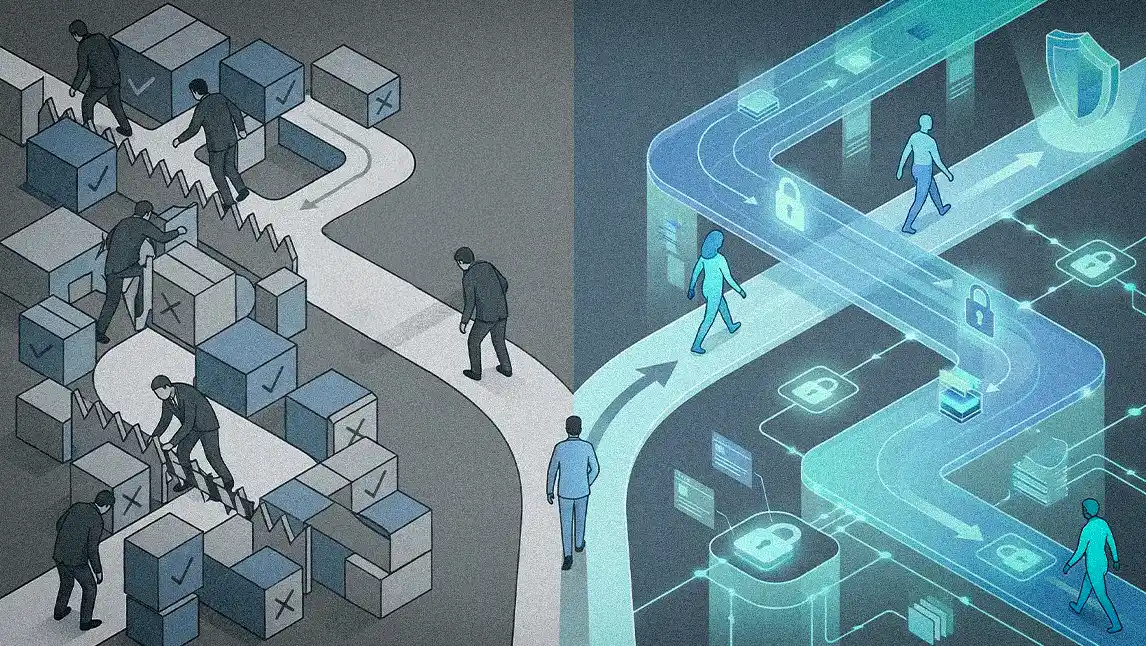
Resilience is not a supporting element of cybersecurity. It is the strategy. The defining question for modern enterprise security is no longer whether attackers can be kept out. It is whether the organization can continue to operate when they get in, and how quickly. AI has not invented new cyberattacks. It has taken familiar attacks like phishing, social engineering, credential abuse, data exfiltration, and put them on fast-forward. Attacks that once took days to plan now materialize in seconds, tailored, convincing, and easy to scale. As that timeline collapses, perimeter defenses alone cannot keep pace, pushing resilience, data recovery, and response speed to the center of modern security strategy.
At the center of this new security strategy is Rick Orloff, VP and CISO of data storage platform provider, Everpure. A seasoned security executive with experience leading programs at Fortune 5-scale organizations, including Apple and eBay, Orloff says that enterprise security can no longer be measured solely by prevention. He believes it must be defined by how quickly an organization can recover, prove what happened, and continue operating when defenses are breached. "Resiliency is the security lens. It's not about checking the right boxes. It's about whether we can take our data, operate somewhere else, and how quickly we can do it," he says.
This distinction matters because the threat environment no longer affords the margins traditional continuity models assume. Resilience today is not about having a plan. It is about execution under pressure, identifying whether critical data can be relocated and restored, whether the organization can operate from an alternate environment, how quickly that happens, and whether leadership can prove what was and was not compromised. AI-powered attacks scale instantly, and recovery timelines measured in days or weeks represent material business impact in most industries. The expectation has shifted to near-immediate restoration of critical systems.
The compressed timeline threat: Orloff's philosophy reflects an environment where the attacker's timeline has collapsed from months to minutes. He describes the traditional model of a fortified perimeter with a soft center as outdated and inherently porous, which is why resilience has become central to defending against modern, AI-powered threats. The enterprise defender must be prepared not only to detect and prevent an attack, but to respond when one gets through. "In that event, you must have the infrastructure, capabilities, and processes in place to recover nearly instantly. The days of thinking we can recover in two weeks simply do not fly anymore," Orloff explains.
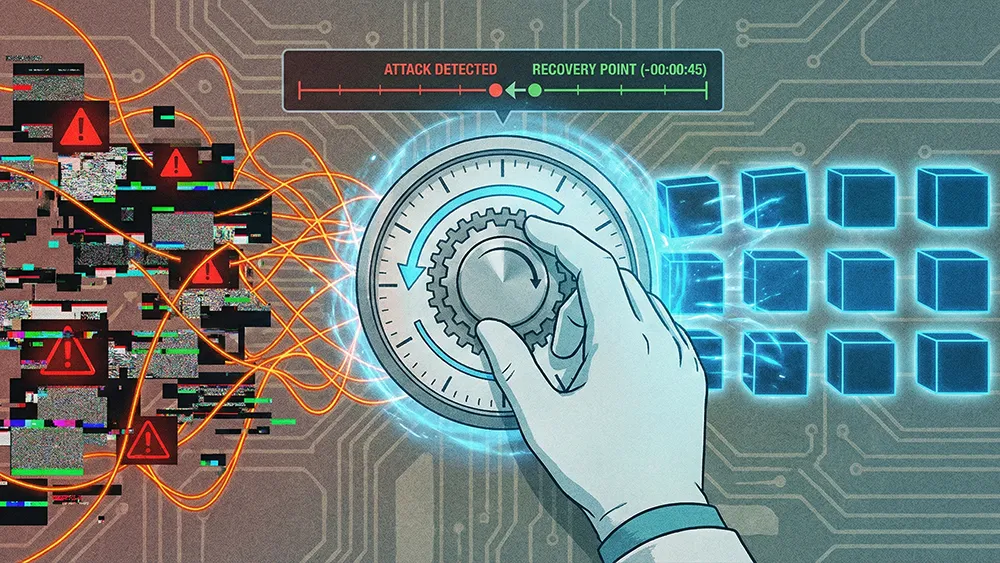
Recovery, covered: Because data is captured continuously at the storage layer, recovery no longer depends on 12-hour backup windows. Orloff calls the ability to recover data from a few seconds or a minute ago a game-changer for organizations accustomed to 12-hour recovery increments. "You can go back in time and choose exactly where you want to recover from, whether it's from three minutes ago or 10 minutes ago," he says. This is strategically significant because the exposure window narrows dramatically, critical systems can be restored with minimal disruption, and leadership can determine with far greater confidence what occurs during an incident.
The forensic dimension of that precision is where resilience becomes a board-level issue rather than an IT concern. Fine-grained recovery gives leadership clarity about what actually occurs during an incident, not just the ability to restore systems. That clarity matters when executive and board attention shifts to liability and exposure, particularly in heavily regulated industries like banking, where legacy infrastructure is under pressure and real-world attacks stop operations entirely.
Room to maneuver: Rapid recovery is not just about speed, but about retaining control as an incident unfolds. "The ability to move and recover means the enterprise maintains flexibility and control. When navigating an incident, we want to establish predictability and outcomes, because often in the recovery process, these quickly become currency," says Orloff. Platforms built around continuous data protection and rapid failover reduce friction between detection and restoration, making resilience a property of the platform rather than a downstream process.
Identify your blast radius: Boards and executive teams should start by identifying which data assets would cause the most damage if compromised. Not all data carries equal enterprise value or risk. The focus belongs on assets that cause material financial harm if confidentiality, integrity, or availability is impacted, systems that halt revenue generation, databases that create regulatory exposure, and intellectual property that defines competitive advantage. Infrastructure can be acquired in an emergency. Hardware can be replaced. The harder question is whether the organization has the data, controls, and processes to land that data elsewhere and keep the business running. "Leaders should be asking, 'Which databases would cause the most pain if leaked or compromised?'" Equally important, when are the dependencies and sub systems needed to operate the business function.
Binary is better: Modern security stacks are dense with layers between the perimeter and the data itself, and every layer introduces potential failure. Orloff advocates stripping that complexity away and securing closer to the source, where outcomes are easier to test and verify. Readiness, he says, should be provable in simple terms. "It's there, or it's not. I can move it or I can't. And if I move it, can I read it and successfully recover? That's a 'yes or no' question." In a board context, that translates to measurable outcomes: recovery time objectives against business tolerance, recovery point objectives in minutes or seconds, and validated restoration testing results.
The shift marks a broader change in how security is evaluated. When companies cannot clearly show what occurs during an incident, exposure is often assumed to be the worst case. Precision recovery changes that dynamic, allowing leaders to demonstrate exactly what data is affected, distinguish between exposure and non-exposure, and support accurate regulatory disclosures rather than defensive ones. The familiar question of whether data is backed up gives way to a more consequential one, whether that data can be used to recover the business and continue serving customers. For public companies, resilience is not a technical feature. It is a governance capability that protects enterprise value when compromise is possible, and timelines are compressed. Orloff concludes, "Security is no longer measured solely by blocked attacks. It is measured by sustained operations under attack."