All articles
Everpure CTO Says Disaster Recovery Alone Leaves Cyber Resilience Exposed
Andrew Stone, CTO for the Americas at Everpure, outlines why treating cyber recovery like disaster recovery leaves organizations dangerously exposed and how to build a truly resilient strategy for modern threats.

Cyber recovery is not disaster recovery. If you’re planning for a tornado, you’re not prepared for an attack. The way these events unfold is completely different, and most teams just aren’t ready to recover in a cyber context.

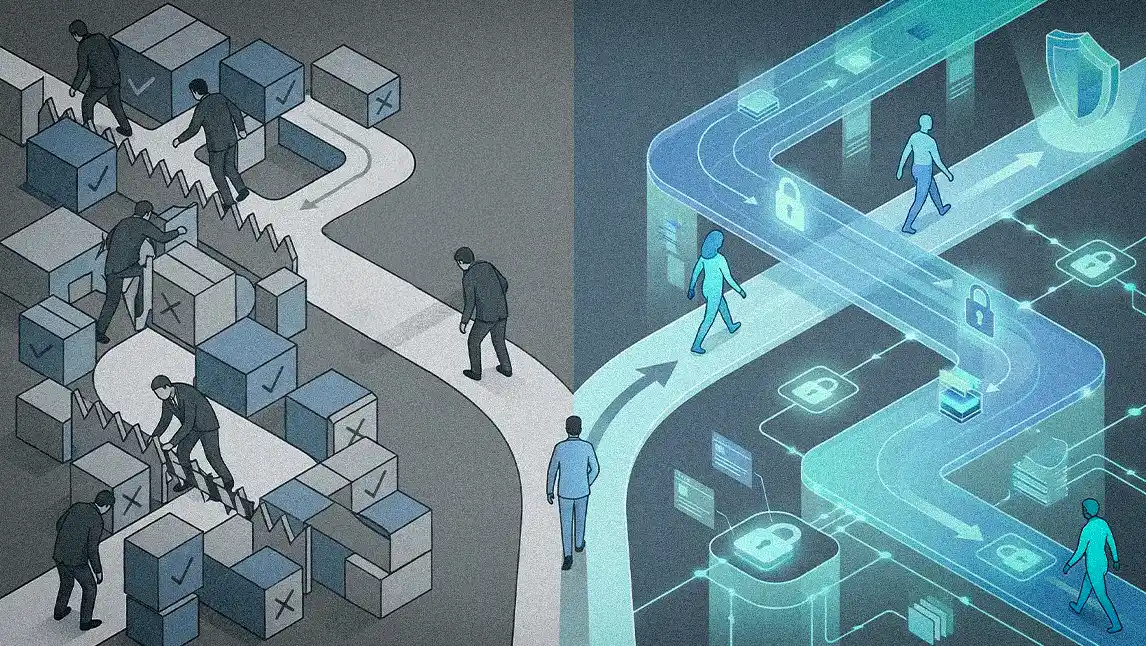
Most cybersecurity strategies are built for the wrong event. The root of the problem is a flawed assumption: that cyber recovery and disaster recovery are the same discipline, but they are not. Modern cyber resilience demands a more focused goal: restoring the "minimum viable business," the core operations needed to keep operating in hours, not days or weeks, rather than full restoration. The result is a costly paradox: organizations are spending heavily on resilience, but remain unable to recover effectively when attacked.
Andrew Stone is CTO for the Americas at Everpure, where he leads technical strategy across data protection, AI security, and cyber resilience. He brings over 25 years of experience as a CISO and technology leader at global firms, including PwC and Farmers Insurance, and holds multiple patents in data protection and security analytics. Stone maintains that most organizations are building resilience strategies that will fail under real-world conditions and won't know it until they're in the middle of an attack.
"Cyber recovery is not disaster recovery. If you’re planning for a tornado, you’re not prepared for an attack," says Stone. "The way these events unfold is completely different, and most teams just aren’t ready to recover in a cyber context." The distinction matters because cyber events demand a different kind of response entirely. Where disaster recovery plans for wholesale restoration, cyber recovery requires speed and precision, focused on getting the most critical operations back online before the damage compounds.
That strategic failure, Stone says, is often rooted in a cultural problem. The pressure to satisfy compliance checklists can come at the expense of building genuine, battle-tested resilience, creating a dangerous illusion of preparedness where policies stand in for actual security outcomes.
A policy's empty promise: "I have never met a compliance standard that has kept an attacker out. No bad guy is going to turn away because you have a 12-character password policy or an untested disaster recovery plan. They simply don't care about those compliance checkboxes." The compliance mindset creates a false baseline where organizations confuse regulatory approval with genuine operational readiness, Stone notes.
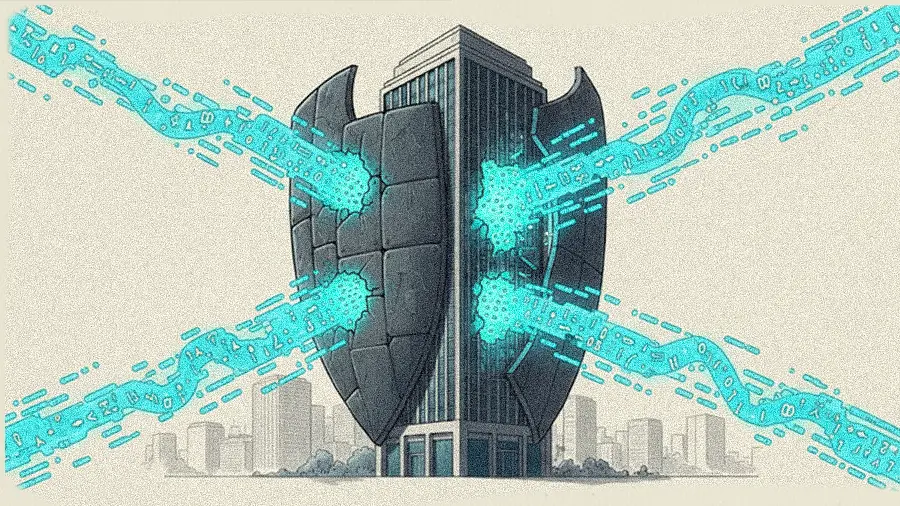
Ransomware's economic motive is a familiar equation. The rise of wiperware, however, changes the dynamic, moving the attacker's primary goal toward pure destruction. As Stone sees it, whether data is encrypted or deleted, the outcome for the business is effectively the same: total inaccessibility. That reality is compounded by the fact that these attacks are becoming more destructive, with nation-state driven actors developing more advanced forms of wipers that target the hardware itself. Yet the greater failure may be that the solutions most organizations rely on to defend against these threats are built on flawed premises.
Burning the building down: "Some of these wipers are built to go after the firmware on hardware devices. Instead of just deleting data, they're going to burn this stuff down," says Stone. "Literally, it's like an attacker burning your building down. They will destroy your infrastructure to the point that you have to buy new kit and rebuild from scratch. A lot of IT teams simply aren't ready for that." Unlike ransomware, which leaves something to negotiate over, firmware-level destruction leaves nothing to recover, making preparation the only viable strategy.
An empty search: Stone notes that several widely accepted security concepts are based on flawed premises, leading teams to invest in solutions that may not work under the pressure of a real attack. He points out that many of these tools are based on a fundamental misunderstanding of how modern malware actually works. "No matter how hard you scan your backups, how many times, or with how many different solutions, you will never find a ransomware payload living on your backups. You might find the result of a ransomware payload living there, like a readme file or encrypted data, but you're not going to find the process itself, again, because it's running in memory on a host." The same logic extends to the backup vendors themselves: exploit kits targeting their known vulnerabilities are openly available, making backups as susceptible to attack as any other part of the infrastructure.
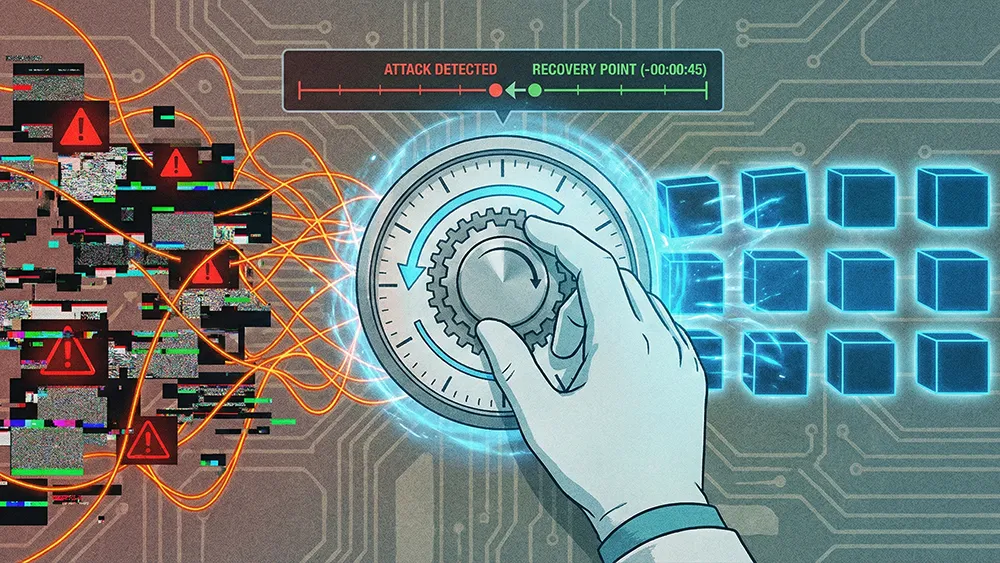
The alternative is a resilient data infrastructure purpose-built for cyber recovery, what Stone calls a Secure Isolated Recovery Environment, or SIRE. Built on a multi-tiered architecture designed for both fast recovery and post-incident investigation, its foundational principle is straightforward: exploits require compute to execute, and a storage environment with no attached compute gives attackers nothing to run against. The first tier, focused on speed, is where Stone takes direct aim at what he calls the "easily defeated" concept of immutability. The architecture also redefines the role traditional backups play and the limits of that role.
An immutable illusion: "The idea of immutability is complete and utter nonsense in this context. Once an attacker gets admin credentials, they can delete your supposedly 'immutable' data," says Stone. "The term only means data can't be changed after it's written. It doesn't mean it can't be deleted. And that's exactly what an attacker will do." That is the gap SafeMode is designed to close, making snapshots not just immutable but indelible, protected even against deletion by a privileged administrator.
Backups in their place: The second tier serves as a "forensics tier," a lower-cost zone for offloaded snapshots held for as long as 180 or 365 days, giving incident response teams the historical data they need. Backups are repurposed for a more fitting role: long-term retention and compliance, a task distinct from the primary cyber recovery path. "Backups should not be used to recover from a cyber event nowadays because they're too slow and they're highly vulnerable to attack. You can go on the dark web and you can buy exploit kits for all the backup vendors," says Stone. "They all have known vulnerabilities, so you can't put all of your eggs in that basket."
While inaction is often blamed on budgetary constraints, Stone says the breakdown is more frequently rooted in poor communication and a failure to frame the business continuity case clearly. When a CISO presents a true cyber recovery option to their board, a solution that might cost a few million dollars but can restore the business in hours versus weeks, the response is almost always an immediate green light.
The board's only question: "When you tell the board you have a way to recover the business in hours instead of weeks, the response is almost always 'Here's the check.' Their only follow-up question will be, 'Is it done yet?'" says Stone. The harder question is why so few CISOs are making that pitch at all, often convinced by market noise that their current setup is good enough when it is not.
Many leaders, overwhelmed by AI and other technologies reshaping the threat landscape, convince themselves their current setup is good enough. The consequences become painfully clear during a real attack, as victims of a recent large-scale destructive incident discovered when their protections crumbled under pressure. "Go ask the victims of that attack how valuable their backups were. I guarantee you they had them," says Stone. "How fast did they get back online? They'll be recovering for a while."
The readiness gap Stone describes runs deeper than most organizations realize, and speaks to internal confusion that compounds the risk. "If you go to most businesses today and ask, 'What are the top 10 applications you absolutely must have to run your business?' 99-plus percent of them couldn't tell you. It's crazy if you think about it," he says.